Building and deploying secure software is no longer an option–it's a necessity. As software applications continue to increase in complexity and interconnectivity, they also pose greater security risks if not developed with care. This is where a Secure Software Development Lifecycle (SSDLC) comes in.
By taking a proactive approach and integrating security efforts throughout the entire development lifecycle, organizations can release better quality software to the market. This prevents security breaches, keeps data safe, and avoids the broader software development risks that compound when vulnerabilities are left unaddressed until after deployment.
This article will provide an overview of what an SSDLC entails, key differences from the traditional SDLC, and the six main phases. It will also explore best practices, and how you can leverage expert guidance to implement a robust SSDLC.
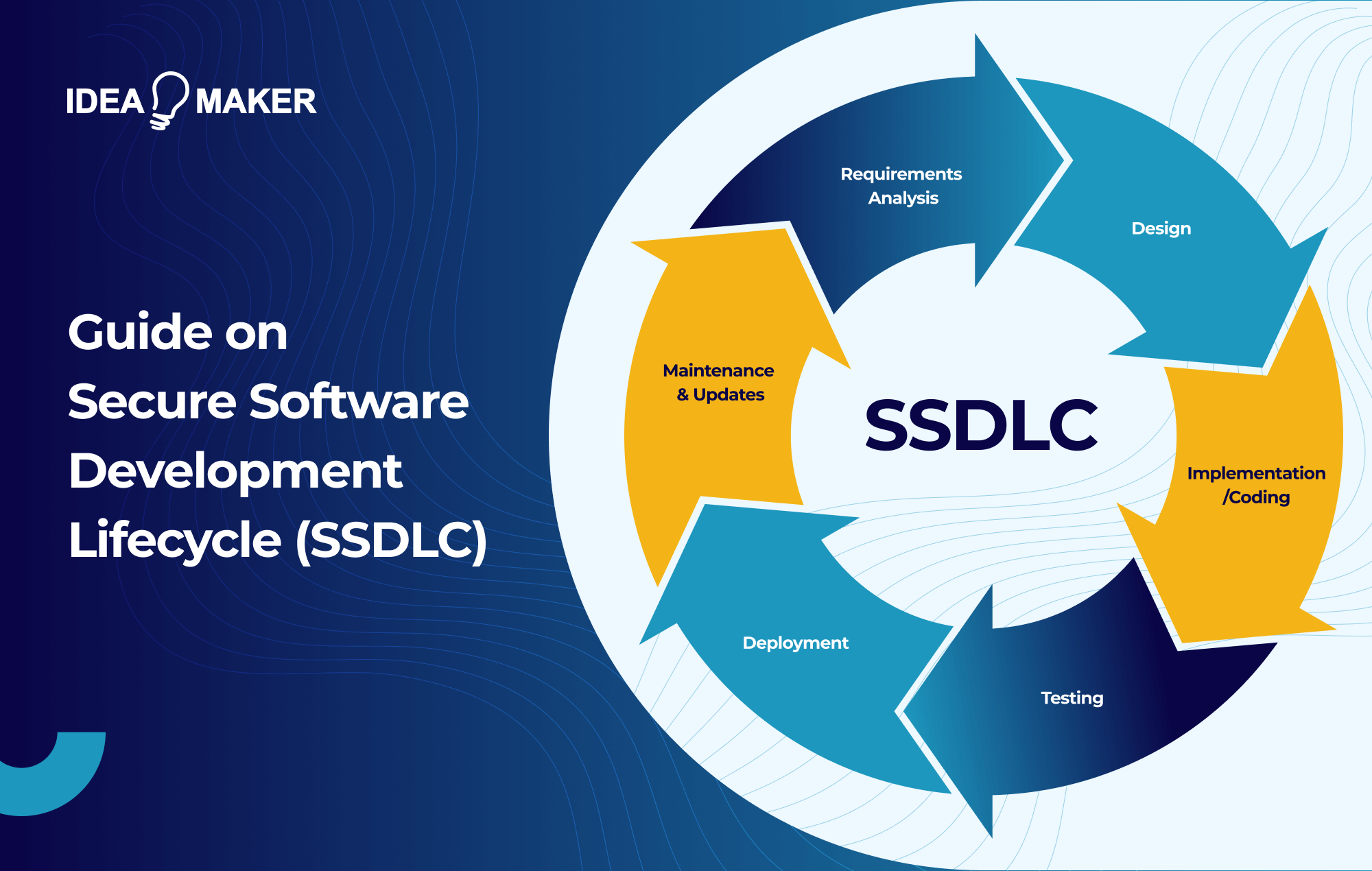
What is Secure Software Development Lifecycle (SSDLC)?
Secure Software Development Lifecycle (SSDLC) is a software development framework in which security requirements, controls, and verification activities are treated as first-class deliverables at every phase, on par with functional requirements. Rather than bolting security on before launch, SSDLC re-engineers each phase of the traditional secure software development SDLC around security as a co-equal objective alongside functionality, performance, and time-to-market.
The defining principle is shift-left security: identifying and addressing vulnerabilities at the earliest possible stage, where they are cheapest to fix and least likely to reach production. A flaw caught during threat modelling in the design phase can cost a fraction of what the same flaw costs to remediate after deployment. Widely cited estimates originating from IBM's Systems Sciences Institute put the gap anywhere from 15x to over 100x, depending on the phase in which the flaw is caught. SSDLC turns that economic reality into a structured methodology.
A record 48,185 CVEs were published in 2025, nearly 4,000 of them rated critical, bringing the global total well past 300,000. With attack surfaces expanding through open-source dependencies, IoT, and AI-driven exploitation, bolting security on at the end of development is no longer viable. SSDLC exists because security has to ship with the code, not after it.
The stakes are highest for enterprise software solutions, where a single application may handle financial records, customer data, and core business operations across thousands of users. A vulnerability in an enterprise system rarely affects just one feature it cascades across integrations, legacy databases, and downstream services, which is why building security into the development lifecycle from day one is no longer optional for organizations operating at this scale.
The outcome of a mature SSDLC is software that is engineered to withstand real-world attacks from day one, protecting customer data, preserving trust, and reducing the business risk that follows every deployment. It is not a compliance exercise or a tooling decision. It is a structural commitment to building software that is secure by design rather than secure by patch.
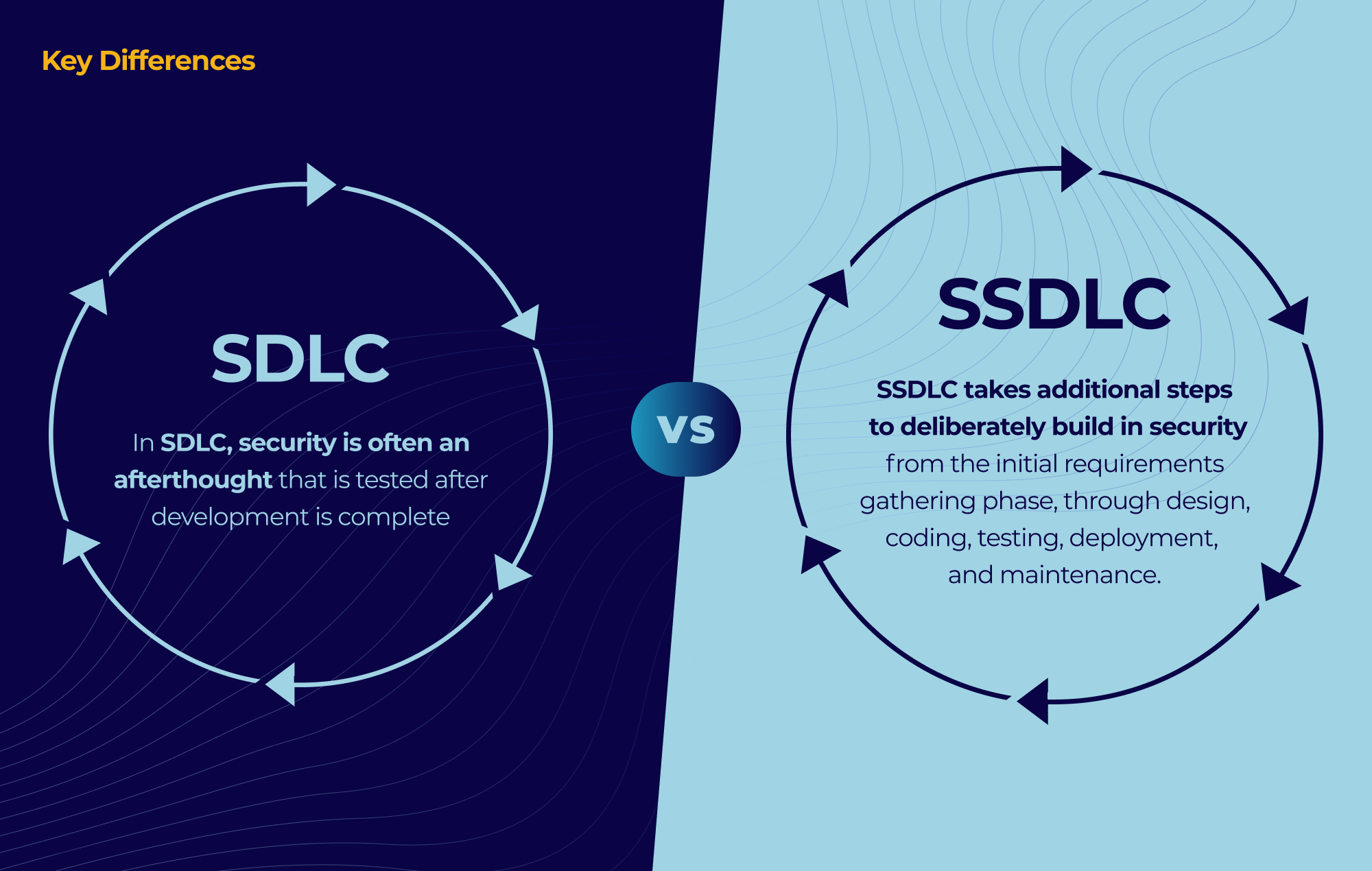
Key Differences Between SSDLC and SDLC (SSDLC vs SDLC)
SSDLC is not a different lifecycle from SDLC it is SDLC re-engineered around the principle that security is a co-equal objective at every phase, not a final checkpoint. The differences are not in what phases exist, but in what happens inside them, who is accountable, and when vulnerabilities are caught. Three dimensions matter most. Here are the key differences between SSDLC and SDLC:
1. When security work happens
In a traditional SDLC, security is typically a pre-launch gate: code is written, features are tested for functionality, and a security review or penetration test happens shortly before release. Anything found at that stage is expensive to fix and often gets deferred to a future sprint.
SSDLC inverts this. Threat modeling happens during requirements. Secure architecture decisions happen during design. SAST runs on every commit during implementation. DAST and pen testing run continuously throughout testing, not just at the end. The economic argument is decisive: long-standing industry estimates suggest fixing a vulnerability during design can cost an order of magnitude less than fixing the same flaw in production. Shift-left is not a slogan; it is the entire business case for SSDLC.
2. What activities exist inside each phase
The phase names are unchanged, but the deliverables expand:
- Requirements: SDLC captures user stories. SSDLC adds abuse cases — the inverse of user stories, describing how an attacker might misuse a feature — along with formal threat modeling and explicit security requirements tied to risk appetite.
- Design: SDLC defines architecture. SSDLC adds attack surface analysis, trust boundary mapping, and secure-by-default configuration choices baked into the data model.
- Implementation: SDLC enforces code style. SSDLC enforces secure coding standards, with SAST and SCA running automatically in CI.
- Testing: SDLC validates functionality. SSDLC adds DAST, fuzzing, dependency scanning, and adversarial pen testing as gating criteria.
- Deployment: SDLC ships the build. SSDLC hardens the runtime, manages secrets, and instruments the environment for continuous monitoring.
- Maintenance: SDLC patches bugs. SSDLC runs vulnerability disclosure programs, monitors threat intelligence feeds for newly disclosed CVEs in dependencies, and feeds incident learnings back into requirements for the next cycle.
| Dimension | Traditional SDLC | SSDLC |
|---|---|---|
| Primary goal | Deliver functional software on time | Deliver functional and secure software on time |
| When security is addressed | Late — typically pre-launch | Continuously — from requirements onward |
| Requirements phase | User stories, functional specs | User stories + abuse cases + threat modeling |
| Design phase | Architecture and data flow | Architecture + attack surface analysis + trust boundaries |
| Implementation phase | Code style and functional standards | Secure coding standards + SAST + SCA in CI |
| Testing phase | Functional and regression testing | Functional testing + DAST + fuzzing + pen testing |
| Deployment phase | Ship the build | Hardened runtime + secrets management + monitoring |
| Maintenance phase | Bug fixes and feature patches | Vulnerability disclosure + threat intel + incident feedback loop |
| Security ownership | Separate security team (gatekeepers) | Shared across product, dev, QA, ops (security as enabler) |
| Cost of fixing vulnerabilities | High — most flaws caught in production | Low — most flaws caught in design or implementation (~30–100x cheaper) |
| Cultural posture | Security as compliance checkpoint | Security as engineering discipline |
| Core question asked | "Does it work?" | "Does it work, and how can it be abused?" |
3. Who owns security
In SDLC, security is typically owned by a separate team that reviews work after the fact — and is often perceived by developers as a blocker. In SSDLC, security is a shared responsibility distributed across product managers, architects, developers, QA, and operations. Security teams shift from gatekeepers to enablers: providing tooling, training, threat models, and security champions embedded inside engineering teams. This cultural change is as important as any technical control — without it, SSDLC processes get worked around rather than adopted.
The result is a fundamentally different posture. SDLC asks "does it work?" SSDLC also asks "how can it be abused, what happens when it is, and how do we know before an attacker tells us?"
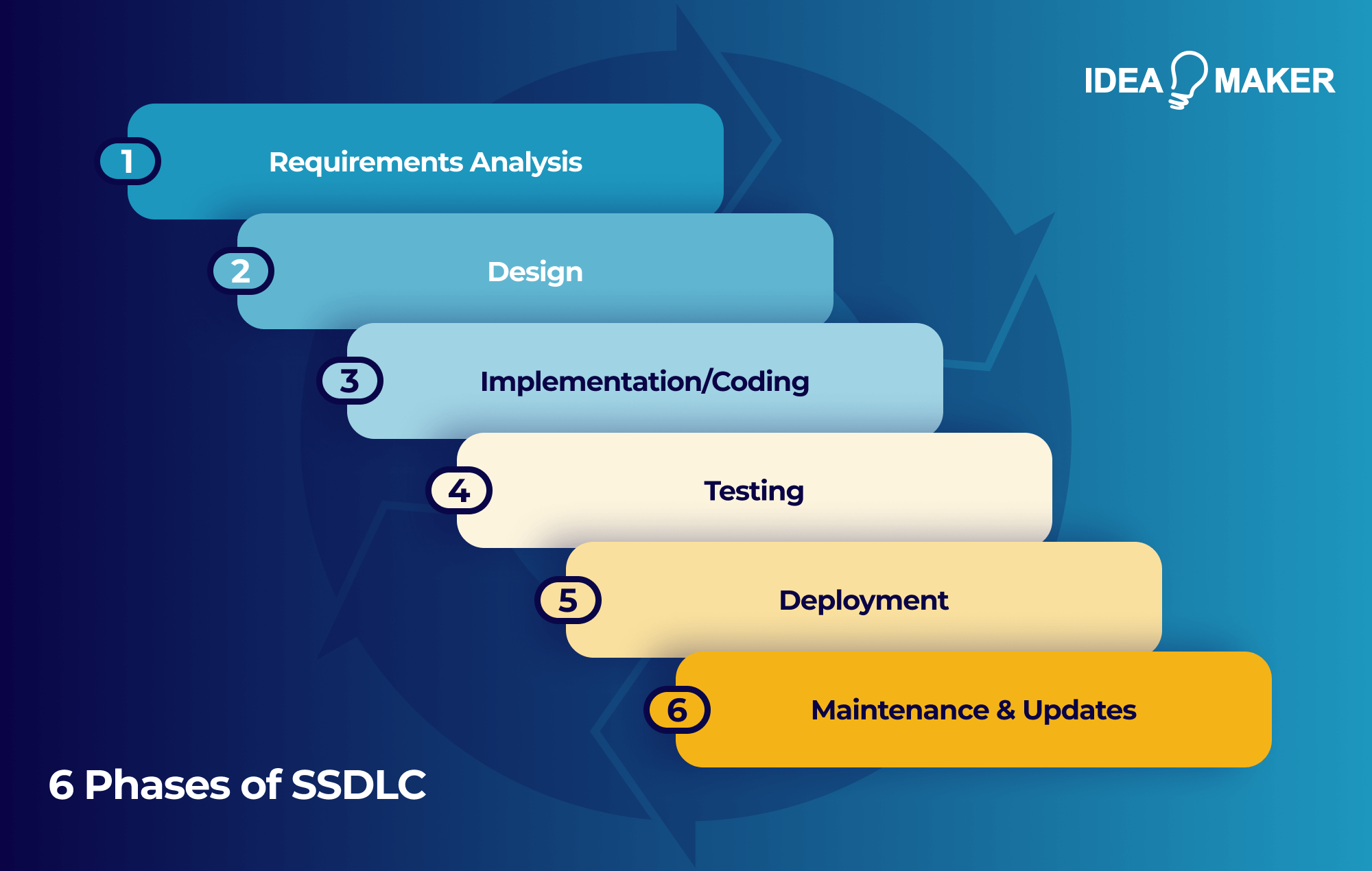
6 Phases of Secure Software Development Lifecycle (SSDLC)
Before walking through the phases, it's worth anchoring SSDLC against the most widely recognized industry standard: NIST Secure Software Development Framework (SP 800-218). NIST SSDF organizes secure development into four practice groups: Prepare the Organization, Protect the Software, Produce Well-Secured Software, and Respond to Vulnerabilities. It is now the de facto reference standard for US federal software procurement and a growing number of enterprise programs. The six phases below map directly to SSDF practices and provide your team with an actionable structure for implementation.
-
Requirements Analysis
This is where SSDLC most visibly diverges from SDLC. Alongside functional user stories, your team captures abuse cases narratives describing how an attacker might misuse a feature and conducts formal threat modeling using a method like STRIDE (Microsoft's categorization model: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege). Having a clearly defined software development plan before this phase begins ensures your team arrives with documented risk appetite, compliance obligations, and security priorities already aligned rather than discovering conflicts mid-requirements gathering.
Compliance requirements such as PCI DSS, HIPAA, GDPR, and SOC 2 are translated into concrete security requirements at this stage. The stakes are particularly high in regulated industries such as software built for financial services, for example, operates under some of the strictest data protection and fraud prevention standards, where a missed compliance requirement at this stage can result in regulatory action post-launch.
-
Design
The design phase focuses on translating security requirements into your software architecture, components, and data flows. Rather than just defining how features will work, your team makes deliberate decisions about how the application will resist attacks from the outset. Encryption choices made at this stage, whether at-rest, in-transit, or field-level, are dramatically cheaper to implement than retrofitting them after launch. Trust boundaries are mapped, the attack surface is enumerated, and secure-by-default configuration choices are baked into the data model rather than left to deployment-time decisions.
Key SSDLC activities undertaken during the design phase include:
- Data flow diagrams: Map how data moves through your application and annotate each flow with trust boundaries to identify where validation and access controls are required.
- Authentication and authorization architecture: Define how users will be authenticated, how sessions will be managed, and how permissions will be enforced across your application.
- Secrets management strategy: Plan how API keys, database credentials, and tokens will be stored, rotated, and accessed without exposure in source code or configuration files.
- Threat model documentation: Produce a formal threat model your engineering team will reference throughout implementation to validate that design assumptions hold as code is written.
- Encryption planning: Decide which data must be encrypted at-rest, in-transit, or at the field level, and select algorithms and key management approaches that align with compliance requirements.
The goal of this phase is to make security an architectural property of your software rather than a feature added later. Decisions made here shape the security posture of every subsequent phase, which is why the design phase is one of the highest-leverage stages in your SSDLC.
-
Implementation/Coding
The implementation phase is where secure design decisions get translated into code. Your developers write against documented secure coding standards whether OWASP, CERT, or language-specific guides and security testing runs automatically in your continuous integration pipeline on every commit rather than as a separate gate. Automation in software development is what makes this continuous validation practical at scale — without it, manual security reviews become bottlenecks that slow delivery rather than protect it The goal is to catch vulnerabilities at the developer's keyboard, when they are easiest and cheapest to fix.
Three categories of tooling matter most during implementation:
- Static Application Security Testing (SAST): Analyzes your source code for injection flaws, buffer issues, and insecure patterns without executing the program. SAST runs on every commit and surfaces issues directly in the developer's pull request.
- Software Composition Analysis (SCA): Scans your third-party and open-source dependencies for known CVEs. According to Black Duck's (formerly Synopsys) Open Source Security and Risk Analysis report, open source makes up roughly 77% of the code in a typical application and is present in 96% of scanned codebases making SCA arguably the highest-leverage tool in your entire SSDLC.
- Secrets scanning: Catches API keys, tokens, and credentials that developers may have accidentally committed to source control before they reach production or end up in public repositories.
Tooling alone is not enough. Mandatory peer code reviews remain essential for catching what automated tools miss, particularly business logic flaws and authorization gaps that require human judgment to identify. Your goal during implementation is to make secure coding the default path for your developers rather than an extra step they have to remember.
-
Testing
The testing phase in SSDLC is layered rather than sequential. Functional QA continues to validate that your software does what it is supposed to do, but it now runs alongside a series of security-focused testing activities designed to validate that your software resists what it is not supposed to do. The goal is to uncover oversights early in the cycle, when they are cheaper to remediate than after deployment.
Several categories of security testing are essential during this phase:
- Dynamic Application Security Testing (DAST): Tests your running application against common attack patterns such as SQL injection, cross-site scripting, and authentication bypass — surfacing vulnerabilities that only appear when code is executing.
- Interactive Application Security Testing (IAST): Instruments your application during testing to combine the depth of SAST with the runtime context of DAST, catching vulnerabilities that either approach alone would miss.
- Fuzzing: Feeds malformed, unexpected, or random inputs into your application to surface edge-case crashes, memory corruption issues, and input validation failures that structured tests would not reach.
- Penetration testing: Engages human testers to simulate real-world attackers, probing your application for chained vulnerabilities, business logic flaws, and creative attack paths that automated tools cannot find.
- Negative testing: Designs explicit test cases intended to break or misuse your application, ensuring that failure modes are handled gracefully rather than exposing sensitive information or crashing in unsafe ways.
Detailed security test cases should be created to validate every authentication path, access control boundary, encryption mechanism, and input validation routine in your application. Findings should flow back to your developers through the same issue tracker as functional bugs rather than living in a separate security backlog that gets deprioritized over time. This is particularly critical when developing enterprise applications, where a single overlooked vulnerability can expose financial records, customer data, and core business workflows across thousands of users at once. Treating security findings as first-class engineering work is what makes the testing phase meaningful in an SSDLC. Treating security findings as first-class engineering work is what makes the testing phase meaningful in an SSDLC.
-
Deployment
The deployment phase in SSDLC is not just about shipping your build to production it is about hardening the runtime environment your software will operate in. A well-structured software deployment plan ensures that security hardening, secrets management, and runtime monitoring are all accounted for before your application faces real-world exposure. As your application transitions from staging to production, your team conducts a comprehensive vulnerability assessment to uncover any security gaps that may have emerged during integration with other systems. Teams managing custom software integration at this stage should ensure that every new connection point is treated as a potential attack surface and hardened accordingly before production exposure. This is your last opportunity to catch high-severity flaws before real-world exposure.
Several SSDLC activities are critical at this stage:
- Infrastructure-as-code scanning: Scan your Terraform, CloudFormation, or Kubernetes manifests for misconfigurations before they are applied to production environments.
- Secrets management: Inject secrets through a dedicated secrets manager rather than environment files or configuration baked into the build.
- Container image signing and scanning: Sign your container images to verify provenance and scan them for known vulnerabilities before they are pulled into production.
- Pre-production penetration testing: Conduct a final adversarial test to validate that integration with downstream systems hasn't introduced new attack paths that were invisible during isolated testing.
- Runtime monitoring instrumentation: Set up application self-protection, anomaly detection, and centralized logging before launch never after.
Once your application is live, your security team should continuously scrutinize user traffic, data flows, access logs, and system activities to detect anomalies that indicate potential attacks before they escalate. eams that are new to this process can benefit from first understanding what software deployment actually entails the configuration, rollback planning, and environment hardening that separates a controlled release from an exposed one.Your production environment is where adversaries focus their efforts, which is why hardening it both before and after release is critical to your SSDLC.
-
Maintenance & Updates
Your work doesn't end once your software is released. The maintenance phase is where SSDLC becomes a true cycle rather than a linear pipeline, and where the long-term security posture of your application is either sustained or eroded over time. This is also where many organizations first recognize the limitations of older systems — security patches become harder to apply, dependencies fall out of support, and vulnerabilities accumulate faster than they can be addressed. In these cases, modernizing legacy applications using SSDLC principles from the ground up is often more sustainable than continuing to patch architecture that was never designed with security in mind.
Four activities run continuously throughout the maintenance phase:
- Vulnerability disclosure program: Operate a public channel through which security researchers can report flaws responsibly rather than disclosing them publicly or selling them on underground markets.
- Threat intelligence monitoring: Track newly disclosed CVEs in your dependencies so that critical patches can be applied within defined service-level agreements before attackers weaponize them.
- Incident response: Maintain documented playbooks, on-call rotations, and blameless post-mortems that ensure your team responds quickly and learns from incidents when they occur.
- Feedback loop into earlier phases: Feed every incident, near-miss, and newly discovered vulnerability class back into your requirements and design phases for the next development cycle.
This last point is what separates a mature SSDLC from a checklist exercise. Lessons from production should flow upstream into how the next feature is built, turning each incident into a permanent improvement rather than a one-time fix. Without this feedback loop, SSDLC becomes just SDLC with extra tools attached. With it, your organization's security posture compounds over time — each cycle leaving your software more resilient than the last.
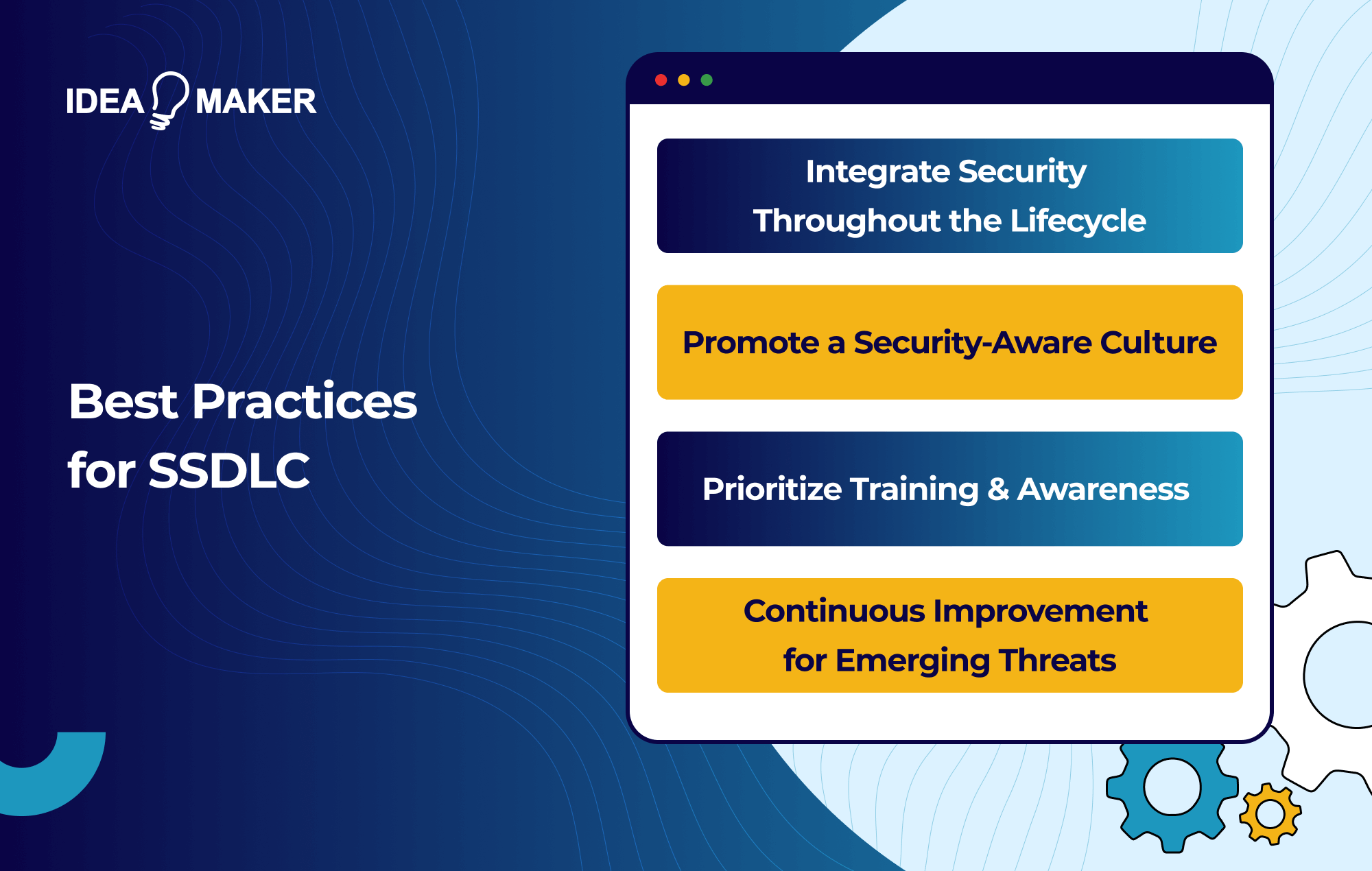
Best Practices for SSDLC
Implementing SSDLC successfully requires more than adopting a phased process — it requires adhering to proven engineering and organizational practices across your entire development lifecycle. Going through the motions of an SSDLC without these underlying principles produces a checklist exercise rather than a meaningful improvement in your security posture. The following best practices distinguish mature SSDLC programs from superficial ones.
Embrace DevSecOps and Shift-Left Security
Modern SSDLC is inseparable from DevSecOps — the practice of embedding security tooling directly into your continuous integration and continuous delivery pipelines so that every commit is scanned, every build is tested, and every deployment is gated by security checks.The right SDLC tools ensure this process runs automatically rather than relying on manual intervention at the end of each sprint. Shift-left means catching issues at the developer's keyboard rather than at the penetration tester's report, weeks or months later when remediation is expensive and disruptive.
Equally critical in 2026 is software supply chain security. Your team should maintain a Software Bill of Materials (SBOM) for every release, sign your build artifacts to verify provenance, and continuously monitor third-party dependencies for newly disclosed vulnerabilities. Following high-profile incidents such as SolarWinds and Log4Shell, SBOM generation has moved from best practice to regulatory requirement — the EU Cyber Resilience Act, taking full effect in 2026, requires manufacturers of digital products to report actively exploited vulnerabilities to authorities within 24 hours of discovery. Your SSDLC must be ready to meet that bar.
Integrate Security Throughout the Lifecycle
Security should be integrated into your entire development lifecycle from initial requirements gathering through to post-deployment monitoring, rather than retrofitted as an afterthought once vulnerabilities surface. Teams that document this as a structured software process with defined security gates at each phase are far less likely to discover critical vulnerabilities late in delivery when remediation is most expensive. It should be treated as an equal priority to functional goals at every phase, not as a gate that work passes through before launch.
Threat modeling should start during requirements and continue to evolve across phases as your understanding of the attack surface deepens. Security-focused code reviews, SAST, SCA, DAST, and penetration testing should all be wired directly into your CI/CD pipelines so that vulnerabilities are caught when they are cheapest to fix. The economic argument is decisive: addressing a flaw during design costs a fraction of what the same flaw costs to remediate in production. Accounting for security tooling and testing as a defined line item in your software budget prevents the far greater cost of emergency remediation after launch.
Build a Security-Aware Culture Through Concrete Artifacts
Transitioning to an SSDLC is not just about process changes — it requires building an organizational culture in which security is treated as a shared responsibility across your developers, architects, QA team, security team, and business leadership. This works best when security is embedded into your development strategy from the outset rather than bolted on as a compliance obligation after delivery commitments are already made. But culture change rarely happens through general statements about "shared responsibility." It happens through specific organizational artifacts that mature SSDLC programs deliberately put in place:
- Security champions programs: Embed a designated security advocate inside each engineering team, providing a local point of contact who bridges the gap between your central security team and day-to-day development work.
- Blameless post-mortems: When incidents occur, focus your analysis on systemic causes and process gaps rather than individual fault, which encourages your engineers to surface near-misses rather than hide them.
- Security OKRs tied to engineering teams: Give your engineering teams measurable security objectives — such as time-to-patch SLAs, percentage of code covered by SAST, or reduction in critical findings per release — rather than treating security as someone else's metric.
- Developer-led threat modeling sessions: Make threat modeling a regular activity led by the engineers building each feature, not a one-time exercise performed by your security team in isolation.
- Executive sponsorship and budget: Ensure your leadership team invests in tooling, ties security to executive metrics, and participates visibly in security reviews so that the organization sees security as a business priority rather than a compliance task.
These artifacts turn cultural intent into operational reality. Without them, security-awareness training and policy documents rarely change behavior on the ground.
Prioritize Training and Continuous Education
Your team should conduct regular secure coding training sessions, workshops, and tabletop exercises to keep developers, QA, and security personnel current on the latest application risks, tools, and remediation techniques. Compliance training on frameworks such as PCI DSS, HIPAA, GDPR, and NIST SSDF should be paired with hands-on coding exercises so that abstract requirements translate into concrete engineering habits.
Focused training helps your team ingrain secure coding habits while empowering them to own security rather than view it as a bottleneck imposed by another team. Prioritizing continuous education is one of the highest-leverage investments your organization can make in the success of your SSDLC.
Continuously Improve for Emerging Threats
The cyber threat landscape evolves rapidly, with attackers innovating new attack vectors faster than most defenses can adapt. Your SSDLC must adapt accordingly through continuous assessment and upgrades rather than periodic audits that quickly become stale.
Your team should learn from past security incidents, near-misses, and external threat intelligence to uncover control gaps and derive insights that strengthen your SSDLC. Iterative improvements to your tooling, processes, and threat models should happen on an ongoing basis — for example, integrating new SCA capabilities as supply chain attacks evolve, or updating threat models as your application architecture changes. The goal is to ensure your SSDLC components continuously improve rather than remaining stagnant after initial implementation. Static security programs lose to dynamic adversaries.
Let Idea Maker Help You With a SSDLC
Most software development agencies treat security as something you add later — or worse, as someone else's problem. At Idea Maker, secure development is built into how we deliver every project, from the first requirements conversation through to launch and beyond.
When we build software for your business, SSDLC principles are part of the engagement by default. This applies whether you are building a consumer-facing product or require dedicated enterprise software development services where compliance, access control, and data protection carry the highest stakes.
- Security requirements captured upfront alongside functional requirements, so there are no surprises late in the project.
- Threat modeling during design to identify risks before a single line of code is written.
- Secure coding standards and code reviews applied throughout development, with SAST and dependency scanning integrated into our pipelines.
- Security testing before launch including penetration testing through trusted partners when your project requires it.
- Documentation and handover that gives your team everything needed to maintain the security posture we build.
Whether you need a new web application, a mobile app, or a custom software built from scratch, Idea Maker delivers software that is engineered to be secure from day one rather than patched after launch. Contact us today to discuss your project and how we can help you ship with confidence.
Frequently Asked Questions
Why is SSDLC required?
SSDLC is required because the cost and frequency of security breaches have made traditional, bolt-on security approaches unsustainable. With a record 48,185 CVEs published in 2025 and attack surfaces expanding through open-source dependencies, IoT devices, and AI-driven exploitation, vulnerabilities discovered after deployment can lead to data breaches, regulatory fines, reputational damage, and loss of customer trust. Beyond the financial impact, modern regulations like the EU Cyber Resilience Act, GDPR, and HIPAA require organizations to demonstrate proactive security practices throughout development — not just at launch. SSDLC provides the structured framework needed to build software that's secure by design, meet compliance obligations, and protect both the business and its users from increasingly sophisticated threats.
How long does it take to transition from SDLC to SSDLC?
There's no fixed timeline — it depends on your team size, codebase complexity, existing tooling, and organizational maturity. Most organizations see meaningful results within 3 to 6 months by starting with high-impact changes like integrating SAST and SCA tools into CI/CD pipelines, then gradually layering in threat modeling, secure code reviews, and cultural changes. Full maturity typically takes 12 to 24 months as processes embed across teams.
Is SSDLC only relevant for large enterprises?
Not at all. While large enterprises often have more resources to invest in dedicated security teams and tooling, SSDLC principles scale down effectively for startups and small businesses. In fact, smaller teams benefit significantly because catching vulnerabilities early prevents costly rework that they often can't afford. Free and open-source tools like OWASP ZAP, Trivy, and GitHub's built-in security features make SSDLC accessible regardless of budget.
How does SSDLC impact development speed and time-to-market?
A common misconception is that SSDLC slows development down. In reality, mature SSDLC programs often accelerate delivery by preventing the costly rework, emergency patches, and incident response that disrupt teams operating without security discipline. Initial adoption may introduce some friction as teams adjust, but once secure practices and automated tooling become routine, velocity typically improves alongside security posture.
What's the difference between SAST, DAST, and IAST?
SAST (Static Application Security Testing) analyzes source code without executing it, catching issues like injection flaws and insecure patterns early in development. DAST (Dynamic Application Security Testing) tests a running application from the outside, simulating real-world attacks on live endpoints. IAST (Interactive Application Security Testing) combines both approaches by instrumenting the application during testing, providing deeper context and fewer false positives than either method alone.
How do I measure the success of an SSDLC program?
Common metrics include mean time to detect (MTTD) and mean time to remediate (MTTR) vulnerabilities, the number of critical findings per release, percentage of code coverage by security tools, time-to-patch SLAs for disclosed CVEs, and the reduction in security incidents over time. Tracking these metrics quarterly helps demonstrate ROI to leadership and identifies areas where your SSDLC needs strengthening.
What is a Software Bill of Materials (SBOM) and why does it matter?
A Software Bill of Materials is a formal inventory of every component, library, and dependency used in your software, including version numbers and licensing information. SBOMs matter because modern applications rely heavily on third-party and open-source code, and knowing exactly what's in your stack is essential for responding to newly disclosed vulnerabilities. Following incidents like Log4Shell, SBOMs have become a regulatory requirement under frameworks like the EU Cyber Resilience Act.
What are the most common mistakes organizations make when adopting SSDLC?
The biggest mistakes include treating SSDLC as a tooling decision rather than a structural commitment, failing to secure executive sponsorship, overwhelming developers with too many tools at once, neglecting training and cultural change, and not establishing a feedback loop from production incidents back into earlier phases. Organizations that succeed treat SSDLC as an ongoing engineering discipline rather than a one-time implementation project.